What you need to know about ‘Juice Jacking’ to stay protected
Summary:
-
Juice Jacking is a real security threat and an official US warning has gone out warning people to avoid public charging stations
-
Criminals can access your data or install malware via a public charging station
-
Stay safe by either using a power outlet or stop data transfer by adding a DataBLOCK between the charging station and your device

Unless you have managed to avoid any news or media outlets in the last while you have no doubt heard the term “juice jacking”. So let’s start with the basics – what is it? Wikipedia offers the following definition:
“Juice jacking is a type of cyber attack involving a charging port that doubles as a data connection, typically over USB. This often involves either installing malware or surreptitiously copying sensitive data from a smart phone, tablet, or other computer device.”
Why is this something you need to know about? Think about the last time you visited a hospital, café or airport lounge. You may have noticed public charging stations. These charging stations have saved me many times when I have been about to run out of battery and need to keep my laptop or phone alive. Powerpoints are just never there when you need them. Unfortunately, these saviours of modern life are now the target for criminals. The attack uses a charging port or infected cable to exfiltrate data from the connected device or upload malware onto it. The term was first used by Brian Krebs in 2011 after a proof of concept was conducted at DEF CON by Wall of Sheep. When users plugged their phones into a free charging station, a message appeared on the kiosk screen saying:
“You should not trust public kiosks with your smart phone. Information can be retrieved or downloaded without your consent. Luckily for you, this station has taken the ethical route and your data is safe. Enjoy the free charge!”
Like scammers who steal debit card numbers by putting illegal card-reading devices, or skimmers, on A.T.M.s, hackers can easily rip out USB ports and replace them with their own malicious hardware, said Vyas Sekar, a professor at CyLab, a security and privacy research institute at Carnegie Mellon University.
“It’s easy to modify the outlet if the attacker has physical access,” Professor Sekar said.
Even a 60-second power-up can be enough to compromise your phone’s data. This is because USB cables allow the transmission of both power and data streams simultaneously. Victims can be left vulnerable to identity theft, financial fraud, and significant stress.
“People want the convenience of charging their phones and tablets wherever they go,” Professor Sekar said, adding, “Obviously I would like it too, but there is a risk.”
Professor Sekar said consumers could also use attachable protective devices on USB cables known as “USB condoms.”
“What they do is a very simple trick,” he said. “They essentially disable the data pin on the USB charger.” This means that the device will charge, but the cable will be unable to send or receive data.
The security threat is so real the Los Angeles District Attorney’s Office issued an advisory to travelers in November 2019 warning them of the potential dangers of using public USB ports.
Malwarebytes Labs explains in more detail how this works:
As you may have noticed, when you charge your phone through the USB port of your computer or laptop, this also opens up the option to move files back and forth between the two systems. That’s because a USB port is not simply a power socket. A regular USB connector has five pins, where only one is needed to charge the receiving end. Two of the others are used by default for data transfers.
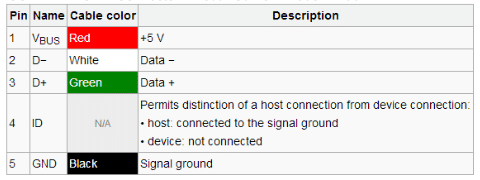
USB Connection table courtesy of Sunrom
Unless you have made changes in your settings, the data transfer mode is disabled by default, except on devices running older Android versions. The connection is only visible on the end that provides the power, which in the case of juice jacking is typically not the device owner. That means, anytime a user connects to a USB port for a charge, they could also be opening up a pathway to move data between devices—a capability threat actors could abuse to steal data or install malware.
There are two ways juice jacking could work:
-
Data theft: During the charge, data is stolen from the connected device.
-
Malware installation: As soon as the connection is established, malware is dropped on the connected device. The malware remains on the device until it is detected and removed by the user.
So how can you tell if you’ve been juice jacked?
Hacked mobile devices will often go undetected. But there are a few telltale signs that your device may have been hacked. These include:
- apps taking a long time to load or frequently crashing
- excessive heating
- An unexpected drain on your battery could indicate a malicious app is now running in the background
- the device running slow or restarting without notice
- updates to device settings that you did not make
- increased or abnormal data usage.
So what is the solution?
If you are keen on the convenience of a charging station and want to avoid being attacked the simplest way is to use a power point or use a USB Data Blocker such as DataBLOCK or DataBLOCK 3 in 1. Described by Professor Sekar as a “USB condom”, the technology in these products prevents accidental data exchange when your device is plugged into someone else’s computer or a public charging station. This is achieved by blocking the data pins on a USB cable and allowing only power to flow through. This minimises the opportunities to steal your data or install malware on your mobile device. They are inexpensive and small, so very easy to carry with you.
