In: In the press
October 30th, 2021
What you need to know about ‘Juice Jacking’ to stay protected
Summary:
-
Juice Jacking is a real security threat and an official US warning has gone out warning people to avoid public charging stations
-
Criminals can access your data or install malware via a public charging station
-
Stay safe by either using a power outlet or stop data transfer by adding a DataBLOCK between the charging station and your device

Unless you have managed to avoid any news or media outlets in the last while you have no doubt heard the term “juice jacking”. So let’s start with the basics – what is it? Wikipedia offers the following definition:
“Juice jacking is a type of cyber attack involving a charging port that doubles as a data connection, typically over USB. This often involves either installing malware or surreptitiously copying sensitive data from a smart phone, tablet, or other computer device.”
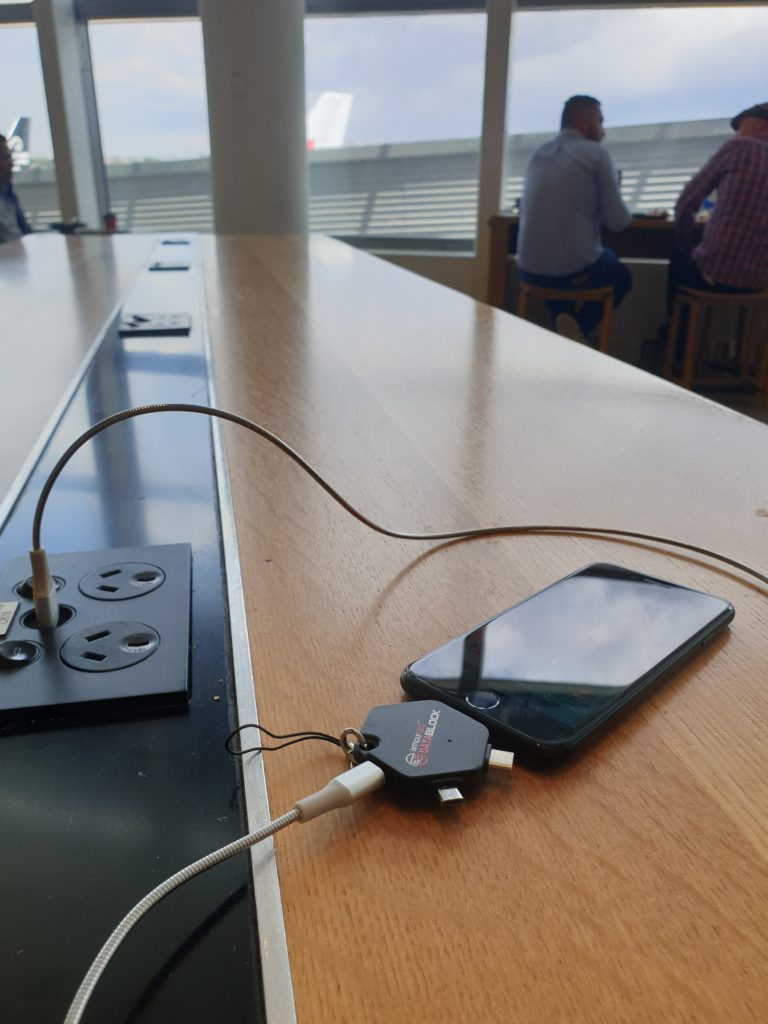
Why is this something you need to know about? Think about the last time you visited a hospital, café or airport lounge. You may have noticed public charging stations. These charging stations have saved me many times when I have been about to run out of battery and need to keep my laptop or phone alive. Powerpoints are just never there when you need them. Unfortunately, these saviours of modern life are now the target for criminals. The attack uses a charging port or infected cable to exfiltrate data from the connected device or upload malware onto it. The term was first used by Brian Krebs in 2011 after a proof of concept was conducted at DEF CON by Wall of Sheep. When users plugged their phones into a free charging station, a message appeared on the kiosk screen saying:
“You should not trust public kiosks with your smart phone. Information can be retrieved or downloaded without your consent. Luckily for you, this station has taken the ethical route and your data is safe. Enjoy the free charge!”
Like scammers who steal debit card numbers by putting illegal card-reading devices, or skimmers, on A.T.M.s, hackers can easily rip out USB ports and replace them with their own malicious hardware, said Vyas Sekar, a professor at CyLab, a security and privacy research institute at Carnegie Mellon University.
“It’s easy to modify the outlet if the attacker has physical access,” Professor Sekar said.
Even a 60-second power-up can be enough to compromise your phone’s data. This is because USB cables allow the transmission of both power and data streams simultaneously. Victims can be left vulnerable to identity theft, financial fraud, and significant stress.
“People want the convenience of charging their phones and tablets wherever they go,” Professor Sekar said, adding, “Obviously I would like it too, but there is a risk.”
Professor Sekar said consumers could also use attachable protective devices on USB cables known as “USB condoms.”
“What they do is a very simple trick,” he said. “They essentially disable the data pin on the USB charger.” This means that the device will charge, but the cable will be unable to send or receive data.
The security threat is so real the Los Angeles District Attorney’s Office issued an advisory to travelers in November 2019 warning them of the potential dangers of using public USB ports.
Malwarebytes Labs explains in more detail how this works:
As you may have noticed, when you charge your phone through the USB port of your computer or laptop, this also opens up the option to move files back and forth between the two systems. That’s because a USB port is not simply a power socket. A regular USB connector has five pins, where only one is needed to charge the receiving end. Two of the others are used by default for data transfers.
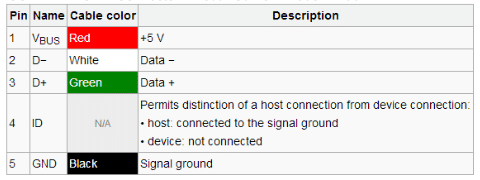
USB Connection table courtesy of Sunrom
Unless you have made changes in your settings, the data transfer mode is disabled by default, except on devices running older Android versions. The connection is only visible on the end that provides the power, which in the case of juice jacking is typically not the device owner. That means, anytime a user connects to a USB port for a charge, they could also be opening up a pathway to move data between devices—a capability threat actors could abuse to steal data or install malware.
There are two ways juice jacking could work:
-
Data theft: During the charge, data is stolen from the connected device.
-
Malware installation: As soon as the connection is established, malware is dropped on the connected device. The malware remains on the device until it is detected and removed by the user.
So how can you tell if you’ve been juice jacked?
Hacked mobile devices will often go undetected. But there are a few telltale signs that your device may have been hacked. These include:
- apps taking a long time to load or frequently crashing
- excessive heating
- An unexpected drain on your battery could indicate a malicious app is now running in the background
- the device running slow or restarting without notice
- updates to device settings that you did not make
- increased or abnormal data usage.
So what is the solution?
If you are keen on the convenience of a charging station and want to avoid being attacked the simplest way is to use a power point or use a USB Data Blocker such as DataBLOCK or DataBLOCK 3 in 1. Described by Professor Sekar as a “USB condom”, the technology in these products prevents accidental data exchange when your device is plugged into someone else’s computer or a public charging station. This is achieved by blocking the data pins on a USB cable and allowing only power to flow through. This minimises the opportunities to steal your data or install malware on your mobile device. They are inexpensive and small, so very easy to carry with you.

August 2nd, 2017
The Australian Newspaper features Armourcard CEO Tyler Harris

 Our CEO Tyler Harris has been featured in the national newspaper The Australian both in print and online on the 1st Aug 2017 in an Article called
Our CEO Tyler Harris has been featured in the national newspaper The Australian both in print and online on the 1st Aug 2017 in an Article called
Armourcard ads to the Arsenal
Mr Harris talked about the next battleground for identity theft and data stolen is on your smartphone and how criminals are exploiting the back door into your phone to get your data.
 Harris went on to say
Harris went on to say
As Australians rely on smartphones to go about their personal and professional transactions, data stored on those devices is the new gold.
and continued
What many people don’t realise is that mobile phones can be penetrated through the NFC technology which is constantly on and emitting a signal. All it takes is for malicious code to be injected through the NFC feature on a smartphone and a hacker pushing out malicious RFID signal to a phone by the RFID chip, to get hold of passwords, photographs, and other personal information.
 Tyler introduced Armourcell, our latest product to protect your android smartphone from this type of attack
Tyler introduced Armourcell, our latest product to protect your android smartphone from this type of attack
With Armourcell, we are providing smartphone users peace of mind and protecting their data from being compromised,
Mr Harris said.
To read the full article please go to The Australian
Find out more about how Armourcell can protect your phone

Australian Financial Review reports on identity theft in the digital age
Tyler Harris the CEO of Armourcard was interviewed for comments by Duncan Hughes the highly respected journalist from the Australian Financial Review on Identity theft and whats coming our way.

You may also like to read about how over 400 mil is wirelessly skimmed from Australians by electronic pickpockets
Find out how you can protect your smartphone with Armourcell
Armourcard has again been featured in the News Limited national Sunday papers across Australia in there travel lift out magazine ‘Escape’ in the travel essentials area ‘What to Pack’ on the 7 August 2016.
Tyler Harris the director went on to say
What a great surprise to be featured again in such a great weekend travel magazine, Escape, that is distributed in all the News Limited Sunday Newspapers
Harris went on to say…
It is a testament to our product offering as being not only the first to produce a Active RFID Micro Jammer in the world but to only offer the most superior protection from this type of invisible crime across a broad spectrum of products from Tap & Go credit cards, ePassports to hotel keys, travel passes and building entry keys that work on the global standard frequency for contact-less devices of 13.56Mhz.
We are a proud Australian company who have invented and patented this technology to help protect your personal information from being skimmed and used often without you ever knowing when or where it happened to you.
You can purchase your Armourcard from our online store or find a local retailer stocking Armourcard near you.
Make sure when you next travel, you travel with the superior protection that only Armourcard can provide.
Stay safe and be vigilant in protecting your data.

Travel Expert and Advice Column Recommends Armourcard to readers.
Acclaimed travel advice column DOC HOLIDAY featured in the Sunday National News Limited newspapers has recommended Armourcard as a must have while travelling.
In the Article Doc Holiday went on to say
I suggest you safeguard yourself for your up coming trip and your everyday movements with one of these cards
The Co Founder of Armourcard Tyler Harris made comments
This was a fantastic surprise to wake up to this article this morning while out having breakfast with my family.
Harris went on to say:
…with a lot of passive card type devices currently flooding the market and being touted trying to blur the lines between their products and our patented technology, we are so pleased to see that the travel professionals who we look to for advice recommend Armourcard as the best product to protect you.
Armourcard is the only product to have FCC (Federal Communication Commission) approval as we needed it as Armourcard emits a “Jamming signal”, we are also TSA approved to go through airport security.
You may also like this article / consumer alert-RFID protect cards are not created equal
[Article appeared in the Doc Holiday expert weekly advice on travel queries feature in the National Sunday News Limited Papers on Sunday 6th March 2016]
To read the article see the newspaper snipet below.

After the US launch of Armourcard at CES 2016 in Las Vegas Nevada earlier this month, it seems we have made quiet an impression with the media and in particular tech writers.
Ben Crosser from PHA media Technology & Innovation team have pulled together a list of Top 10 Safety & Security Companies to Watch at CES 2016
Ben intro’s the piece
Another year, another CES, brimming with start-ups and household names alike, looking to become the next big tech trend. But who will come out victorious? In the third of a six-part series, we give our verdict on the most awe-inspiring hopefuls of the New Year in the Safety & Security category.
Ben goes on the say:
CES in Las Vegas is a haven of game-changing companies and products – not least in the safety & security sector. Throughout 2015 we saw hundreds of headlines that both highlighted vulnerabilities and emphasised the need for viable solutions – from cyber security to child safety.
And continues…
From over 500 impressive companies exhibiting at CES from 6-8 January, we have identified a list of 10 to keep an eye on in 2016, as they look to revolutionise the safety & security industry as we know it.
At Armourcard we are so thrilled to be included on such a prestigious list.
One of Armourcard’s founders Tyler Harris responded to the news …
It’s fantastic to see that we have made an impression at the worlds largest Consumer Electronic Show, it is a testament to all the hard work both the Australian and our US associates have put in to get us to the show. The feedback, retail opportunities from launching Armourcard and the new soon to be released Armourcell product on the global stage has really been exciting.

Harris added…
The year ahead is already shaping up to be very busy, with the heightened interest in both our products generated from our launch at CES we are already in talks with some exciting potential retail opportunities both in the US and abroad off the back of the show.
The full article can be Read here
If you are interested in stocking Armourcard please enquire here via our contact us page
January 20th, 2016
CES 2016 – iTProTV interviews us on the stand

Armourcard gets featured on iTProTV live stream at CES2016 Las Vegas Nevada
 With the dust barley settling after Consumer Electronic Show in Las Vegas we thought it might be a good time to share some of the media and attention Armourcard got for the US launch and iTProTV is the first off the rank.
With the dust barley settling after Consumer Electronic Show in Las Vegas we thought it might be a good time to share some of the media and attention Armourcard got for the US launch and iTProTV is the first off the rank.
CES2016 was the US launch of Armourcard and we generated a lot of interest in our jamming technology. The stand often had 20 people crowded around watching the demonstration and how Armourcard offers the most superior active electronic protection on the market today.
iTProTv’s host Don Pezet approached us for a live on-air stream interview on the first day of the show.
Here is one of our Founders Tyler Harris explaining a little bit about the skimming problem and how Armourcard’s active jamming solution is the ‘end game’ for your protection.
There is no better protection than electronically jamming the communication link these devices talk over, that is what Armourcard does.
 Armourcard is the only RFID protective product certified by Federal Communication Commission (FCC), we had to be as we emit a signal and that signal is jamming the frequency 13.56Mhz which is the most common frequency contactless devices like credit cards, ePassports, building entry cards & NFC phones use to communicate over.
Armourcard is the only RFID protective product certified by Federal Communication Commission (FCC), we had to be as we emit a signal and that signal is jamming the frequency 13.56Mhz which is the most common frequency contactless devices like credit cards, ePassports, building entry cards & NFC phones use to communicate over.
Armourcard has FCC certification
Thanks Don and all the iTProTv team for stopping by and featuring us on your great Technology TV show.
December 21st, 2015
APC magazine review Armourcard as a travel essential

Armourcard review by APC magazine
APC or Australian Personal Computing has featured Armourcard in a recent article on travel goods and travel essentials.
Lindsay Handmer one of the journalists at APC reviewed Armourcard and tested and gave a very good review of 4 stars.
(in-fact no product got a higher score from all the products reviewed.)
Next time you travel the article that reviews Armourcard as an essential travel good to take with you, especially with ePassports, tap & go credit / debit cards and many hotel keys able to be skimmed.
Don’t travel without one, the Armourcard reviews say.
To read the full review Read APC article
August 21st, 2015
Armourcard Featured on SKY NEWS Money Exchange show

SKY NEWS Money interviews Tyler Harris
On Friday 21st August 2015, one of Armourcard’s Directors Tyler Harris was asked to be a guest speaker on SKY NEWS MONEY the Money Exchange show with Andrew Barnett.
The interview titled:
Electronic Pick Pocketing. What is it and how to avoid it?
In the interview Tyler was asked by Andrew from the Money Exchange one of SKY NEWS money segments some key questions surrounding the topic ranging from:
What is electronic pick pocketing and how prevalent is it?
right through to…
So when they scan my details what do they get and how can they use it?
In the live on-air filming of SKY NEWS Money Exchange Show with Andrew Barnett, Harris went on to say:
Its not just about credit cards and fiscal loss off a card, the bigger picture is profiling you for identity theft.
He also went on to say:
Identity theft is a growing global concern
And as more of this type of technology comes into our lives we must start to protect ourselves from exploitation of the very same technology found in these tap & go credits and ePassports.
Watch the SKY NEWS Money Exchange segment above, the interview starts at 2:47 in the video.
June 19th, 2015
Armourcard featured on channel Nine’s A Current Affair show

Channel Nine’s A Current Affair show ran a story on Tap & Go Fraud
A big thank you to Tracy Grimshaw & Trevor Long for featuring on ACA Armourcard and a running a great story raising awareness of the vulnerabilities surrounding the technology that most of us already have in our wallets and purses.
Trevor Long went on to show how easy it was with freely available software on an NFC enabled smartphone to actually skim credit card details of a card.
As Ben mentioned in the report, the criminals use better equipment than a smartphone and will be able to skim you from a greater distance just like brushing past you in the street or on public transport
or in your local shopping mall.
Your personal data can be skimmed and sent instantly across the other side of the world to clone onto a mag-stripe card.
Trevor also mentioned that this technology becoming more accepted into our lives could open the floodgates to profiling your data for more identity theft-related crimes.
Tyler Harris, Armourcard CEO was featured showing how an Australian invention is helping prevent this wireless skimming crime by our product Armourcard.
Armourcard is the only product in the world to actively jam the frequency (or communication link) between your credit cards and the criminals with readers trying to wirelessly skim your data.